How APNS works with MDMs that manage OSX and iOS
Classic Environment
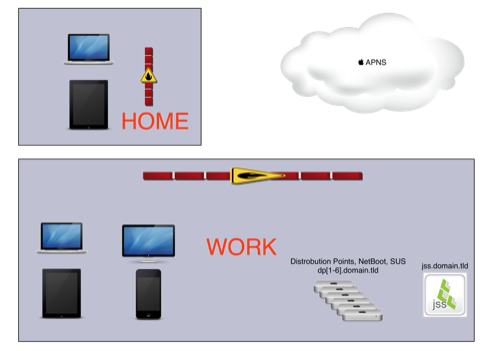
- “Work” location where your MDM (CasperSuite JSS in this example), and other internal servers may exist.
- “Home” location because people take their equipment home and still do work from the comforts of their couch.
APNS Workflow
This is where the magic happens!
You as the OS X and/or iOS Administrator want your devices to do something. It may be install a Configuration Profile to “lock down”, OR provide a feature such as Email configuration, Wi-Fi Access, or something else… but you want it down NOW! You login to your MDM management page/console, select what devices you want to perform some action. At that point, your MDM does the following:
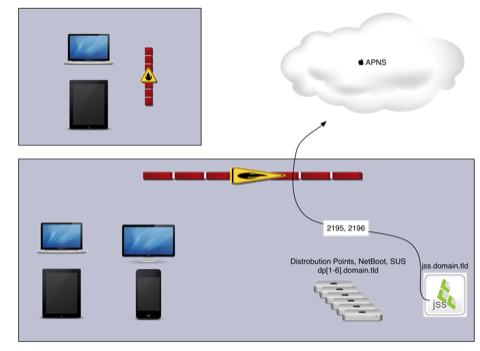
- Communicate to Apple’s Push Notification Servers (APNS) over ports 2195, and 2196 to “FIND MY DEVICES”.
- Your devices are already connected to APNS once they turn on, they have Internet connection, AND port 5223 is not blocked. When your device does connect to Apple’s APNS network, it gets a token.
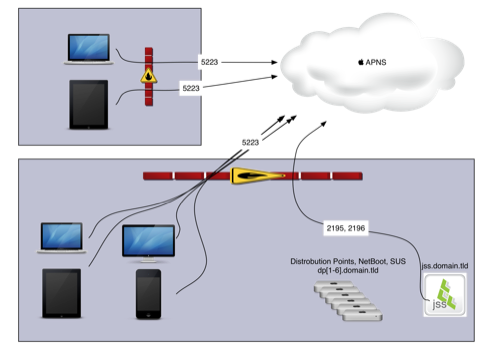
- It’s this token that allows Apple’s APNS network to find and talk to your devices through your firewall. They key element is when APNS push commands are sent, the only bits of information in the payload from Apple is “HEY Device! Talk to your MDM” and nothing else. That is where APNS stops being the middle man and let’s a secure communication take over between your devices and MDM only.
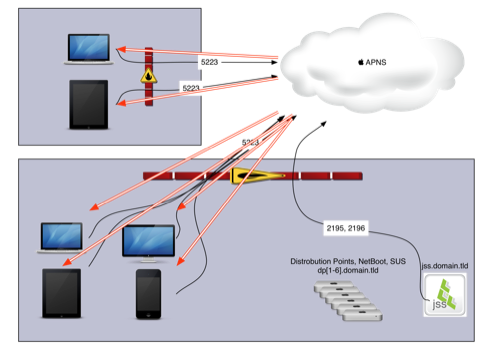
- Once the devices received that command, they will then talk to your MDM over their designated port for the next set of commands you wish to execute from the MDM. In my example commands are sent over port 8443 as this is the port for the Casper Suite (but it may be 443 for other MDM’s such as Profile Manager).
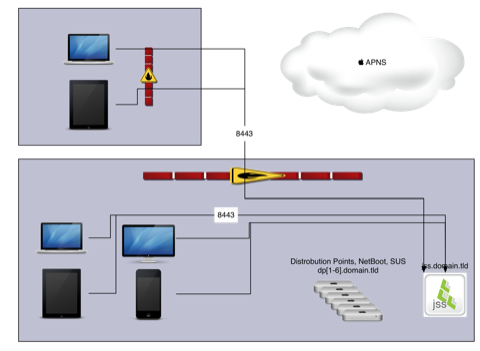
- Your devices then do whatever your MDM requests.
Examples
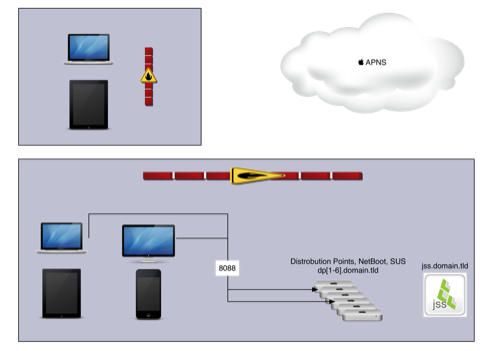
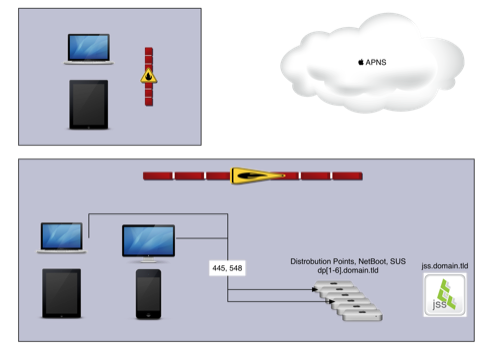
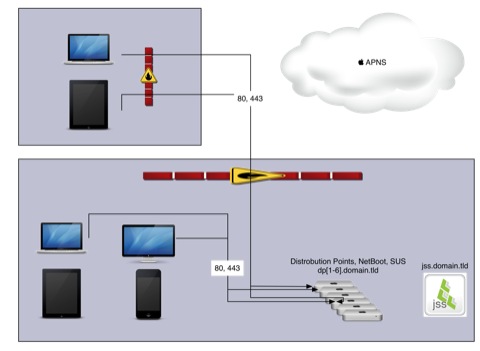
Some examples that the JSS can do to help manage your OSX environment include:
- Request to get Software Updates from your Internal SUS over port 8088
- Install packages from an SMB (445) or AFP (548) FileShare
- Install packages from an HTTP (80) or HTTPS (443) server. 1
- Force NetBoot, but I’m not going into the port numbers for that as there are too many.
Sources
- Apple’s Developer Documentation on APNS
- About push Notification; Advance Administration guide
- Apple’s list of Ports for APNS
- Apple’s NetBoot troubleshooting
- Well known TCP and UDP ports used by Apple
Footnotes
-
Be sure your Certificate on your HTTPS distribution point is signed by a third-party OR that your internal ROOT CA is already installed on your client machines. ↩



Comments are closed. If you have a question concerning the content of this page, please feel free to contact me.